2019-10-01 15:40:17 +02:00
|
|
|
// Copyright 2019 The Gitea Authors. All rights reserved.
|
2022-11-27 19:20:29 +01:00
|
|
|
// SPDX-License-Identifier: MIT
|
2019-10-01 15:40:17 +02:00
|
|
|
|
|
|
|
|
package mirror
|
|
|
|
|
|
|
|
|
|
import (
|
2019-12-15 10:51:28 +01:00
|
|
|
"context"
|
2019-10-01 15:40:17 +02:00
|
|
|
"fmt"
|
|
|
|
|
|

feat(quota): Quota enforcement
The previous commit laid out the foundation of the quota engine, this
one builds on top of it, and implements the actual enforcement.
Enforcement happens at the route decoration level, whenever possible. In
case of the API, when over quota, a 413 error is returned, with an
appropriate JSON payload. In case of web routes, a 413 HTML page is
rendered with similar information.
This implementation is for a **soft quota**: quota usage is checked
before an operation is to be performed, and the operation is *only*
denied if the user is already over quota. This makes it possible to go
over quota, but has the significant advantage of being practically
implementable within the current Forgejo architecture.
The goal of enforcement is to deny actions that can make the user go
over quota, and allow the rest. As such, deleting things should - in
almost all cases - be possible. A prime exemption is deleting files via
the web ui: that creates a new commit, which in turn increases repo
size, thus, is denied if the user is over quota.
Limitations
-----------
Because we generally work at a route decorator level, and rarely
look *into* the operation itself, `size:repos:public` and
`size:repos:private` are not enforced at this level, the engine enforces
against `size:repos:all`. This will be improved in the future.
AGit does not play very well with this system, because AGit PRs count
toward the repo they're opened against, while in the GitHub-style fork +
pull model, it counts against the fork. This too, can be improved in the
future.
There's very little done on the UI side to guard against going over
quota. What this patch implements, is enforcement, not prevention. The
UI will still let you *try* operations that *will* result in a denial.
Signed-off-by: Gergely Nagy <forgejo@gergo.csillger.hu>
2024-07-06 10:30:16 +02:00
|
|
|
quota_model "code.gitea.io/gitea/models/quota"
|
2021-12-10 02:27:50 +01:00
|
|
|
repo_model "code.gitea.io/gitea/models/repo"
|
2020-01-14 04:38:04 +01:00
|
|
|
"code.gitea.io/gitea/modules/graceful"
|
2019-10-01 15:40:17 +02:00
|
|
|
"code.gitea.io/gitea/modules/log"
|
2021-10-17 13:43:25 +02:00
|
|
|
"code.gitea.io/gitea/modules/queue"
|
2019-10-01 15:40:17 +02:00
|
|
|
"code.gitea.io/gitea/modules/setting"
|
|
|
|
|
)
|
|
|
|
|
|
2021-10-17 13:43:25 +02:00
|
|
|
// doMirrorSync causes this request to mirror itself
|
2023-08-27 04:24:45 +02:00
|
|
|
func doMirrorSync(ctx context.Context, req *SyncRequest) {
|
2022-03-02 08:43:11 +01:00
|
|
|
if req.ReferenceID == 0 {
|
|
|
|
|
log.Warn("Skipping mirror sync request, no mirror ID was specified")
|
|
|
|
|
return
|
|
|
|
|
}
|
2021-10-17 13:43:25 +02:00
|
|
|
switch req.Type {
|
2023-08-27 04:24:45 +02:00
|
|
|
case PushMirrorType:
|
2022-03-02 08:43:11 +01:00
|
|
|
_ = SyncPushMirror(ctx, req.ReferenceID)
|
2023-08-27 04:24:45 +02:00
|
|
|
case PullMirrorType:
|
2022-03-02 08:43:11 +01:00
|
|
|
_ = SyncPullMirror(ctx, req.ReferenceID)
|
2021-10-17 13:43:25 +02:00
|
|
|
default:
|
2022-03-02 08:43:11 +01:00
|
|
|
log.Error("Unknown Request type in queue: %v for MirrorID[%d]", req.Type, req.ReferenceID)
|
2021-10-17 13:43:25 +02:00
|
|
|
}
|
|
|
|
|
}
|
2019-10-01 15:40:17 +02:00
|
|
|
|
2021-11-23 04:09:35 +01:00
|
|
|
var errLimit = fmt.Errorf("reached limit")
|
|
|
|
|
|
2019-10-01 15:40:17 +02:00
|
|
|
// Update checks and updates mirror repositories.
|
2021-11-23 04:09:35 +01:00
|
|
|
func Update(ctx context.Context, pullLimit, pushLimit int) error {
|
2021-09-07 17:49:36 +02:00
|
|
|
if !setting.Mirror.Enabled {
|
|
|
|
|
log.Warn("Mirror feature disabled, but cron job enabled: skip update")
|
|
|
|
|
return nil
|
|
|
|
|
}
|
2019-10-01 15:40:17 +02:00
|
|
|
log.Trace("Doing: Update")
|
2021-06-14 19:20:43 +02:00
|
|
|
|
2024-04-27 12:44:49 +02:00
|
|
|
handler := func(bean any) error {
|
2022-02-08 15:02:32 +01:00
|
|
|
var repo *repo_model.Repository
|
2023-08-27 04:24:45 +02:00
|
|
|
var mirrorType SyncType
|
2022-07-08 21:45:12 +02:00
|
|
|
var referenceID int64
|
|
|
|
|
|
2021-12-10 02:27:50 +01:00
|
|
|
if m, ok := bean.(*repo_model.Mirror); ok {
|
2023-09-29 14:12:54 +02:00
|
|
|
if m.GetRepository(ctx) == nil {
|
2021-06-14 19:20:43 +02:00
|
|
|
log.Error("Disconnected mirror found: %d", m.ID)
|
|
|
|
|
return nil
|
|
|
|
|
}
|
2022-02-08 15:02:32 +01:00
|
|
|
repo = m.Repo
|
2023-08-27 04:24:45 +02:00
|
|
|
mirrorType = PullMirrorType
|
2022-07-08 21:45:12 +02:00
|
|
|
referenceID = m.RepoID
|
2021-12-10 02:27:50 +01:00
|
|
|
} else if m, ok := bean.(*repo_model.PushMirror); ok {
|
2023-10-03 12:30:41 +02:00
|
|
|
if m.GetRepository(ctx) == nil {
|
2021-06-14 19:20:43 +02:00
|
|
|
log.Error("Disconnected push-mirror found: %d", m.ID)
|
|
|
|
|
return nil
|
|
|
|
|
}
|
2022-02-08 15:02:32 +01:00
|
|
|
repo = m.Repo
|
2023-08-27 04:24:45 +02:00
|
|
|
mirrorType = PushMirrorType
|
2022-07-08 21:45:12 +02:00
|
|
|
referenceID = m.ID
|
2021-06-14 19:20:43 +02:00
|
|
|
} else {
|
|
|
|
|
log.Error("Unknown bean: %v", bean)
|
2019-10-01 15:40:17 +02:00
|
|
|
return nil
|
|
|
|
|
}
|
2021-06-14 19:20:43 +02:00
|
|
|
|
2021-11-23 04:09:35 +01:00
|
|
|
// Check we've not been cancelled
|
2019-12-15 10:51:28 +01:00
|
|
|
select {
|
|
|
|
|
case <-ctx.Done():
|
2021-11-23 04:09:35 +01:00
|
|
|
return fmt.Errorf("aborted")
|
2019-12-15 10:51:28 +01:00
|
|
|
default:
|
|
|
|
|
}
|
2021-11-23 04:09:35 +01:00
|
|
|
|

feat(quota): Quota enforcement
The previous commit laid out the foundation of the quota engine, this
one builds on top of it, and implements the actual enforcement.
Enforcement happens at the route decoration level, whenever possible. In
case of the API, when over quota, a 413 error is returned, with an
appropriate JSON payload. In case of web routes, a 413 HTML page is
rendered with similar information.
This implementation is for a **soft quota**: quota usage is checked
before an operation is to be performed, and the operation is *only*
denied if the user is already over quota. This makes it possible to go
over quota, but has the significant advantage of being practically
implementable within the current Forgejo architecture.
The goal of enforcement is to deny actions that can make the user go
over quota, and allow the rest. As such, deleting things should - in
almost all cases - be possible. A prime exemption is deleting files via
the web ui: that creates a new commit, which in turn increases repo
size, thus, is denied if the user is over quota.
Limitations
-----------
Because we generally work at a route decorator level, and rarely
look *into* the operation itself, `size:repos:public` and
`size:repos:private` are not enforced at this level, the engine enforces
against `size:repos:all`. This will be improved in the future.
AGit does not play very well with this system, because AGit PRs count
toward the repo they're opened against, while in the GitHub-style fork +
pull model, it counts against the fork. This too, can be improved in the
future.
There's very little done on the UI side to guard against going over
quota. What this patch implements, is enforcement, not prevention. The
UI will still let you *try* operations that *will* result in a denial.
Signed-off-by: Gergely Nagy <forgejo@gergo.csillger.hu>
2024-07-06 10:30:16 +02:00
|
|
|
// Check if the repo's owner is over quota, for pull mirrors
|
|
|
|
|
if mirrorType == PullMirrorType {
|
|
|
|
|
ok, err := quota_model.EvaluateForUser(ctx, repo.OwnerID, quota_model.LimitSubjectSizeReposAll)
|
|
|
|
|
if err != nil {
|
|
|
|
|
log.Error("quota_model.EvaluateForUser: %v", err)
|
|
|
|
|
return err
|
|
|
|
|
}
|
|
|
|
|
if !ok {
|
|
|
|
|
log.Trace("Owner quota exceeded for %-v, not syncing", repo)
|
|
|
|
|
return nil
|
|
|
|
|
}
|
|
|
|
|
}
|
|
|
|
|
|
2021-11-23 04:09:35 +01:00
|
|
|
// Push to the Queue
|
2023-08-27 04:24:45 +02:00
|
|
|
if err := PushToQueue(mirrorType, referenceID); err != nil {
|
2022-02-08 15:02:32 +01:00
|
|
|
if err == queue.ErrAlreadyInQueue {
|
2023-08-27 04:24:45 +02:00
|
|
|
if mirrorType == PushMirrorType {
|
2022-02-08 15:02:32 +01:00
|
|
|
log.Trace("PushMirrors for %-v already queued for sync", repo)
|
|
|
|
|
} else {
|
|
|
|
|
log.Trace("PullMirrors for %-v already queued for sync", repo)
|
|
|
|
|
}
|
|
|
|
|
return nil
|
|
|
|
|
}
|
2021-11-23 04:09:35 +01:00
|
|
|
return err
|
|
|
|
|
}
|
|
|
|
|
return nil
|
2021-06-14 19:20:43 +02:00
|
|
|
}
|
|
|
|
|
|
2022-02-08 15:02:32 +01:00
|
|
|
pullMirrorsRequested := 0
|
2021-11-23 04:09:35 +01:00
|
|
|
if pullLimit != 0 {
|
2024-04-29 10:47:56 +02:00
|
|
|
if err := repo_model.MirrorsIterate(ctx, pullLimit, func(_ int, bean any) error {
|
2024-04-27 12:44:49 +02:00
|
|
|
if err := handler(bean); err != nil {
|
2022-02-28 20:41:06 +01:00
|
|
|
return err
|
|
|
|
|
}
|
|
|
|
|
pullMirrorsRequested++
|
|
|
|
|
return nil
|
2021-11-23 04:09:35 +01:00
|
|
|
}); err != nil && err != errLimit {
|
|
|
|
|
log.Error("MirrorsIterate: %v", err)
|
|
|
|
|
return err
|
|
|
|
|
}
|
2021-06-14 19:20:43 +02:00
|
|
|
}
|
2022-02-28 20:41:06 +01:00
|
|
|
|
2022-02-08 15:02:32 +01:00
|
|
|
pushMirrorsRequested := 0
|
2021-11-23 04:09:35 +01:00
|
|
|
if pushLimit != 0 {
|
2023-07-04 20:36:08 +02:00
|
|
|
if err := repo_model.PushMirrorsIterate(ctx, pushLimit, func(idx int, bean any) error {
|
2024-04-27 12:44:49 +02:00
|
|
|
if err := handler(bean); err != nil {
|
2022-02-28 20:41:06 +01:00
|
|
|
return err
|
|
|
|
|
}
|
|
|
|
|
pushMirrorsRequested++
|
|
|
|
|
return nil
|
2021-11-23 04:09:35 +01:00
|
|
|
}); err != nil && err != errLimit {
|
|
|
|
|
log.Error("PushMirrorsIterate: %v", err)
|
|
|
|
|
return err
|
|
|
|
|
}
|
2019-10-01 15:40:17 +02:00
|
|
|
}
|
2022-02-08 15:02:32 +01:00
|
|
|
log.Trace("Finished: Update: %d pull mirrors and %d push mirrors queued", pullMirrorsRequested, pushMirrorsRequested)
|
2020-05-17 01:31:38 +02:00
|
|
|
return nil
|
2019-10-01 15:40:17 +02:00
|
|
|
}
|
|
|
|
|
|
2023-08-27 04:24:45 +02:00
|
|
|
func queueHandler(items ...*SyncRequest) []*SyncRequest {
|

Rewrite queue (#24505)
# ⚠️ Breaking
Many deprecated queue config options are removed (actually, they should
have been removed in 1.18/1.19).
If you see the fatal message when starting Gitea: "Please update your
app.ini to remove deprecated config options", please follow the error
messages to remove these options from your app.ini.
Example:
```
2023/05/06 19:39:22 [E] Removed queue option: `[indexer].ISSUE_INDEXER_QUEUE_TYPE`. Use new options in `[queue.issue_indexer]`
2023/05/06 19:39:22 [E] Removed queue option: `[indexer].UPDATE_BUFFER_LEN`. Use new options in `[queue.issue_indexer]`
2023/05/06 19:39:22 [F] Please update your app.ini to remove deprecated config options
```
Many options in `[queue]` are are dropped, including:
`WRAP_IF_NECESSARY`, `MAX_ATTEMPTS`, `TIMEOUT`, `WORKERS`,
`BLOCK_TIMEOUT`, `BOOST_TIMEOUT`, `BOOST_WORKERS`, they can be removed
from app.ini.
# The problem
The old queue package has some legacy problems:
* complexity: I doubt few people could tell how it works.
* maintainability: Too many channels and mutex/cond are mixed together,
too many different structs/interfaces depends each other.
* stability: due to the complexity & maintainability, sometimes there
are strange bugs and difficult to debug, and some code doesn't have test
(indeed some code is difficult to test because a lot of things are mixed
together).
* general applicability: although it is called "queue", its behavior is
not a well-known queue.
* scalability: it doesn't seem easy to make it work with a cluster
without breaking its behaviors.
It came from some very old code to "avoid breaking", however, its
technical debt is too heavy now. It's a good time to introduce a better
"queue" package.
# The new queue package
It keeps using old config and concept as much as possible.
* It only contains two major kinds of concepts:
* The "base queue": channel, levelqueue, redis
* They have the same abstraction, the same interface, and they are
tested by the same testing code.
* The "WokerPoolQueue", it uses the "base queue" to provide "worker
pool" function, calls the "handler" to process the data in the base
queue.
* The new code doesn't do "PushBack"
* Think about a queue with many workers, the "PushBack" can't guarantee
the order for re-queued unhandled items, so in new code it just does
"normal push"
* The new code doesn't do "pause/resume"
* The "pause/resume" was designed to handle some handler's failure: eg:
document indexer (elasticsearch) is down
* If a queue is paused for long time, either the producers blocks or the
new items are dropped.
* The new code doesn't do such "pause/resume" trick, it's not a common
queue's behavior and it doesn't help much.
* If there are unhandled items, the "push" function just blocks for a
few seconds and then re-queue them and retry.
* The new code doesn't do "worker booster"
* Gitea's queue's handlers are light functions, the cost is only the
go-routine, so it doesn't make sense to "boost" them.
* The new code only use "max worker number" to limit the concurrent
workers.
* The new "Push" never blocks forever
* Instead of creating more and more blocking goroutines, return an error
is more friendly to the server and to the end user.
There are more details in code comments: eg: the "Flush" problem, the
strange "code.index" hanging problem, the "immediate" queue problem.
Almost ready for review.
TODO:
* [x] add some necessary comments during review
* [x] add some more tests if necessary
* [x] update documents and config options
* [x] test max worker / active worker
* [x] re-run the CI tasks to see whether any test is flaky
* [x] improve the `handleOldLengthConfiguration` to provide more
friendly messages
* [x] fine tune default config values (eg: length?)
## Code coverage:
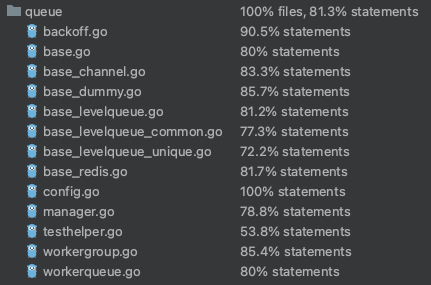
2023-05-08 13:49:59 +02:00
|
|
|
for _, req := range items {
|
2021-10-17 13:43:25 +02:00
|
|
|
doMirrorSync(graceful.GetManager().ShutdownContext(), req)
|
2019-10-01 15:40:17 +02:00
|
|
|
}
|
2022-01-22 22:22:14 +01:00
|
|
|
return nil
|
2020-10-25 08:32:25 +01:00
|
|
|
}
|
|
|
|
|
|
2019-10-01 15:40:17 +02:00
|
|
|
// InitSyncMirrors initializes a go routine to sync the mirrors
|
|
|
|
|
func InitSyncMirrors() {
|
2023-08-27 04:24:45 +02:00
|
|
|
StartSyncMirrors(queueHandler)
|
2019-10-01 15:40:17 +02:00
|
|
|
}
|